Accelerate Security Testing with a Reversing AI Agent
Understand third-party and supply chain software faster, even without source code or symbols

Finding Security Insights Starts with Understanding Complex Binaries
Security teams often spend a significant portion of their time making unfamiliar software binaries understandable before meaningful testing can begin. Third-party and supply chain components, complex codebases, and missing context make it difficult to trace behavior and follow dataflows. Identifying the code paths most relevant to a security assessment becomes slow and manual. As software complexity grows, producing clear, evidence-based findings becomes harder without extensive reversing.
Make your Software Security Assessments Exceptionally Productive
Zenyard provides deep binary understanding through purpose-built AI agents that analyze entire files end-to-end. It enables incident response and security assessment teams to quickly make sense of unfamiliar binaries, including third-party and software supply chain software, trace behavior and dataflow, and identify the code paths most relevant to their investigation. With Zenyard, teams can explain findings with concrete evidence, prioritize the parts of the software that matter most, and deliver report-ready findings and assessment deliverables with higher confidence and less manual reverse engineering.
Deploy Zenyard Securely, Your Way
Deploy fully on-premises, even within air-gapped networks
Deploy within your own fully controlled cloud environment
The New Way to Understand Third-Party Software
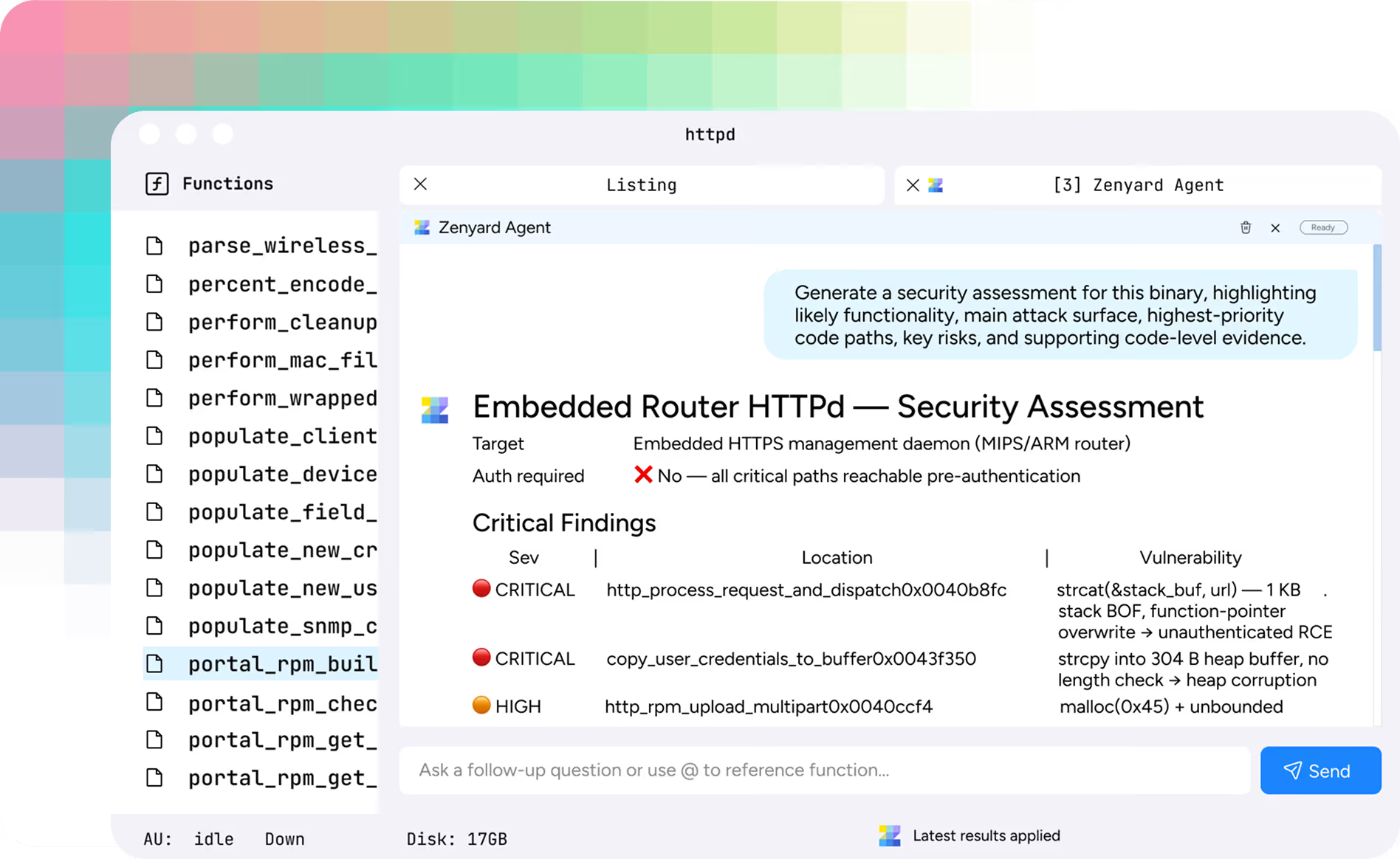
Accelerate black-box software
assessments and reduce reversing time
Analyze entire binaries
to ensure all critical context is captured
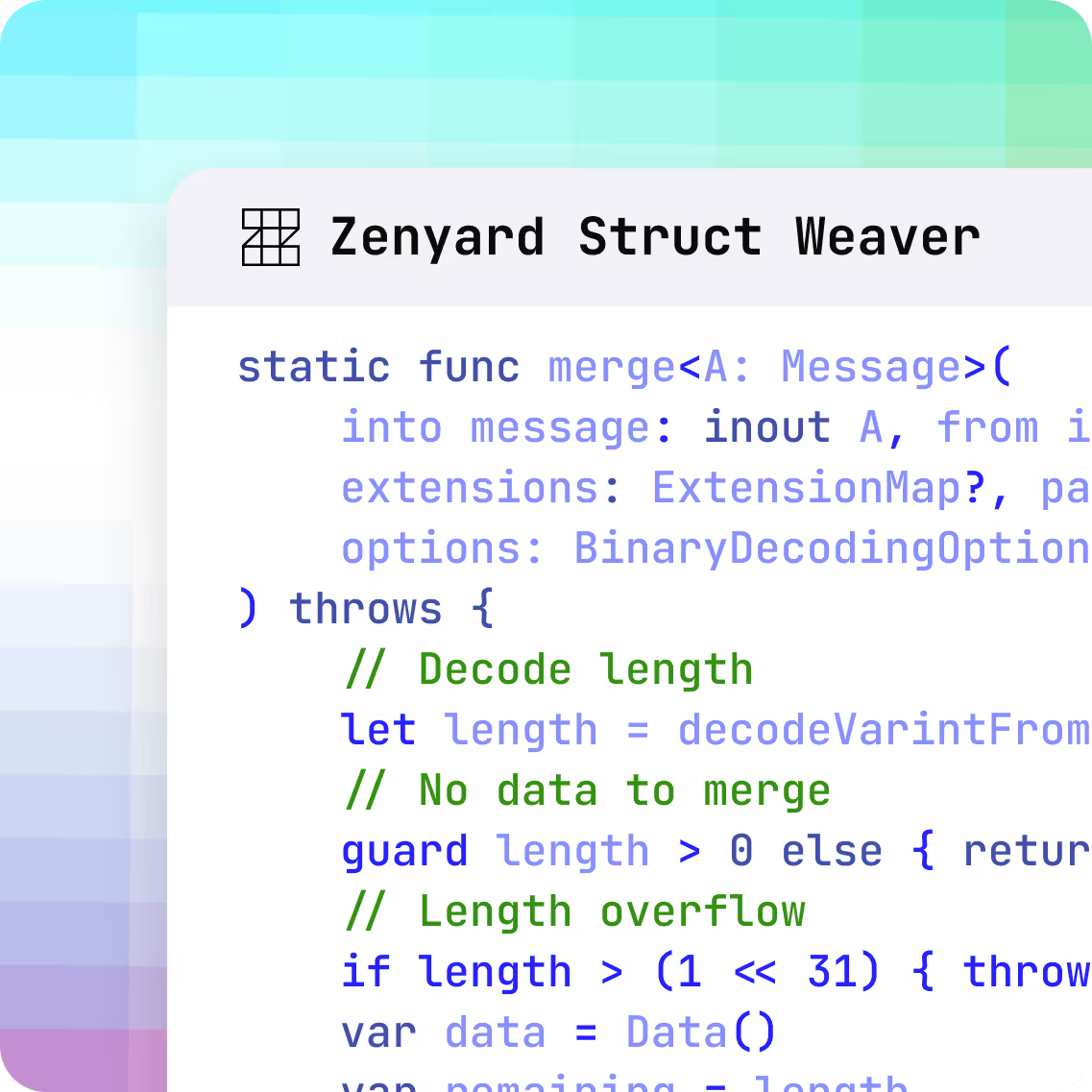
Transform stripped software into
fully named, documented, source-like code
Surface relevant code paths
for faster security assessment
Quickly understand complex code
and generate research reports
Explain findings
with concrete code-level evidence
From Decompiled Code to Insights You Can Trust

Comprehensive end-to-end file understanding
Support for complex embedded and third-party software targets
Whole program struct reconstruction
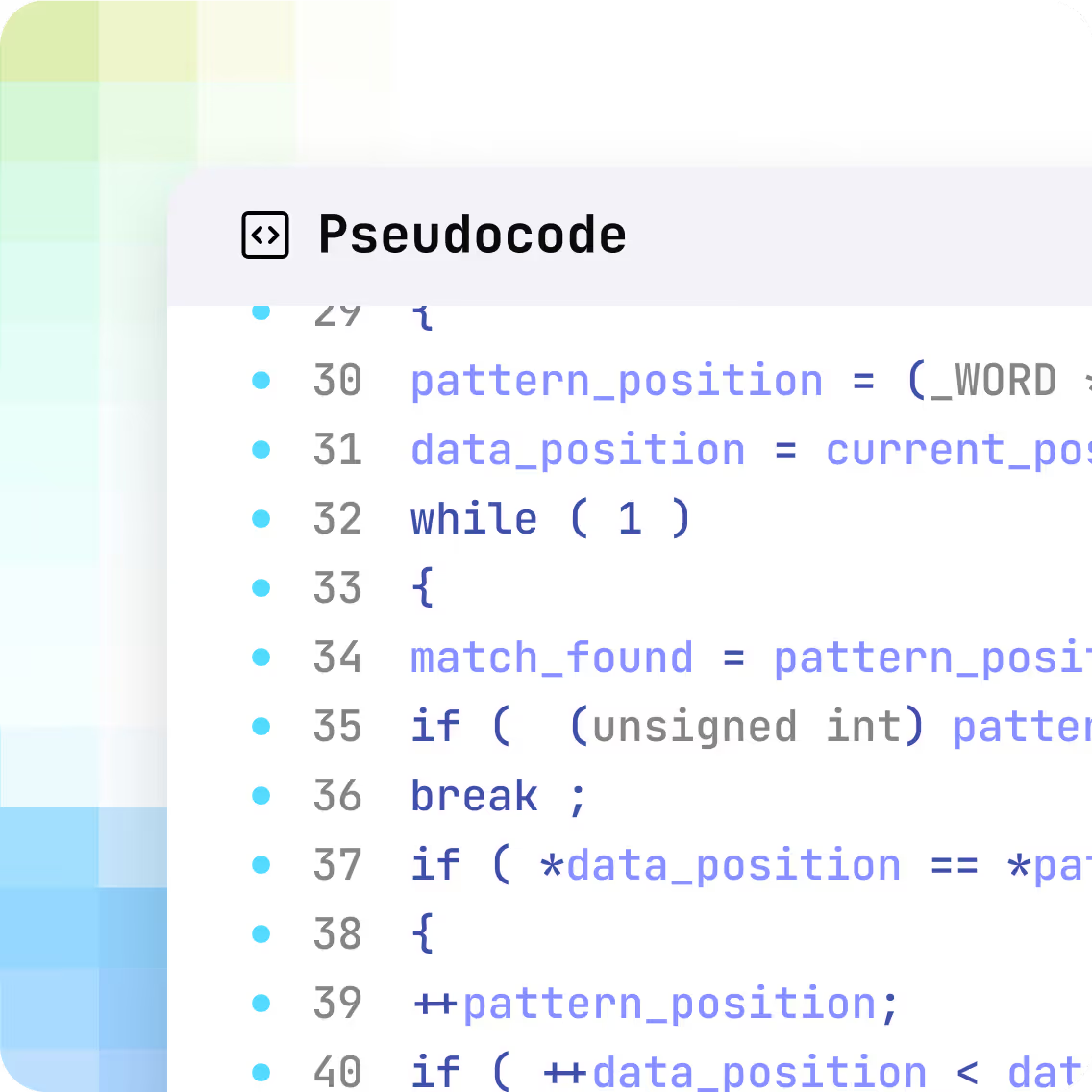
Decompiled code is read like source

Direct integration with existing decompilers