Accelerate Malware Analysis with a Reversing AI Agent
Analyze and triage malware samples faster, even when binaries are obfuscated and complex

Finding Security Insights Starts with Understanding Complex Binaries
Most of a security researcher’s day is spent getting a malware sample into a readable state. This includes handling obfuscation, analyzing complex Go and Rust binaries, and reconstructing data structures by hand. As samples become more complex, AI tools struggle to maintain context, producing shallow or unreliable results exactly when deep analysis matters most. This slows down malware triage and increases time to insight across the analysis workflow.
Make Your Malware Analysis Exceptionally Productive
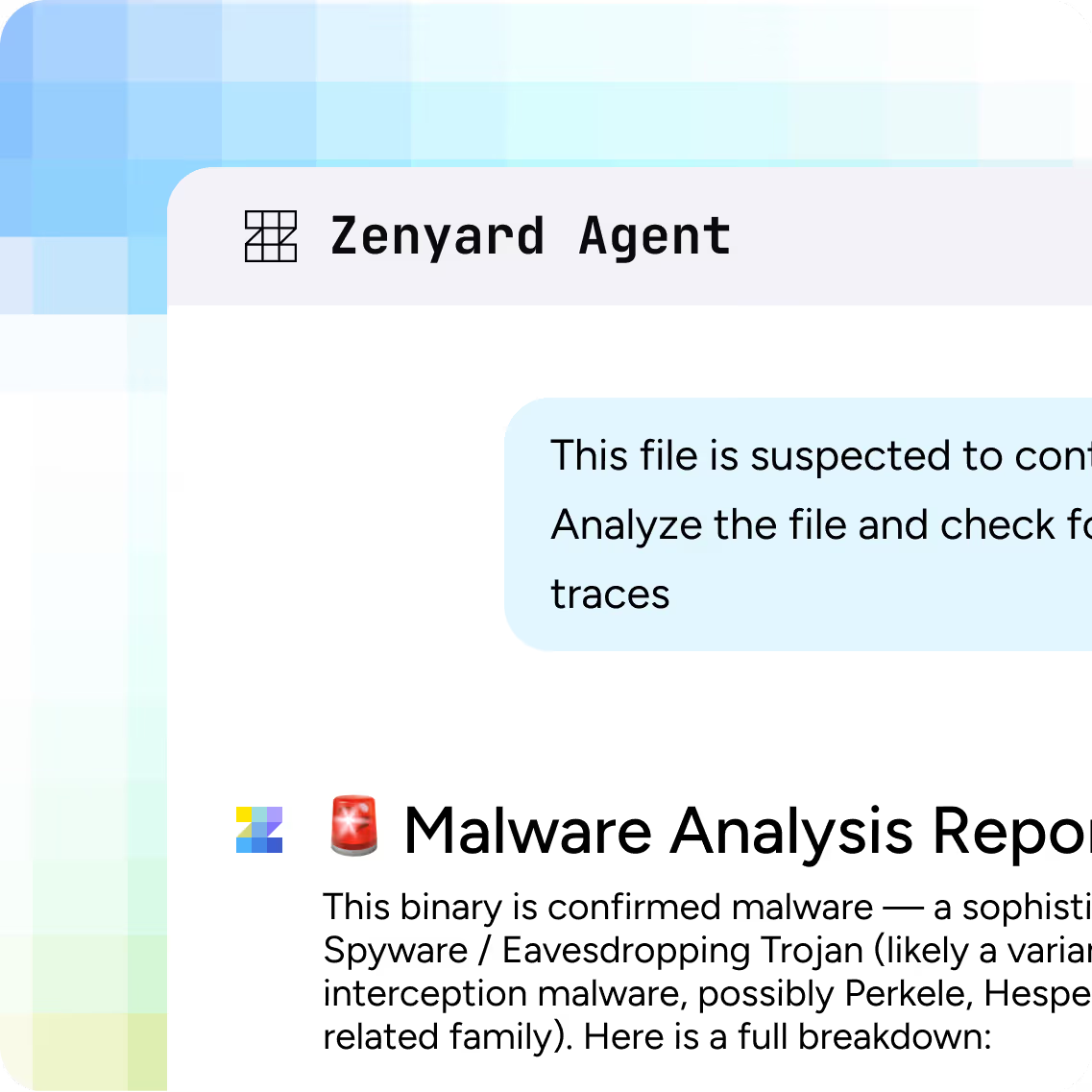
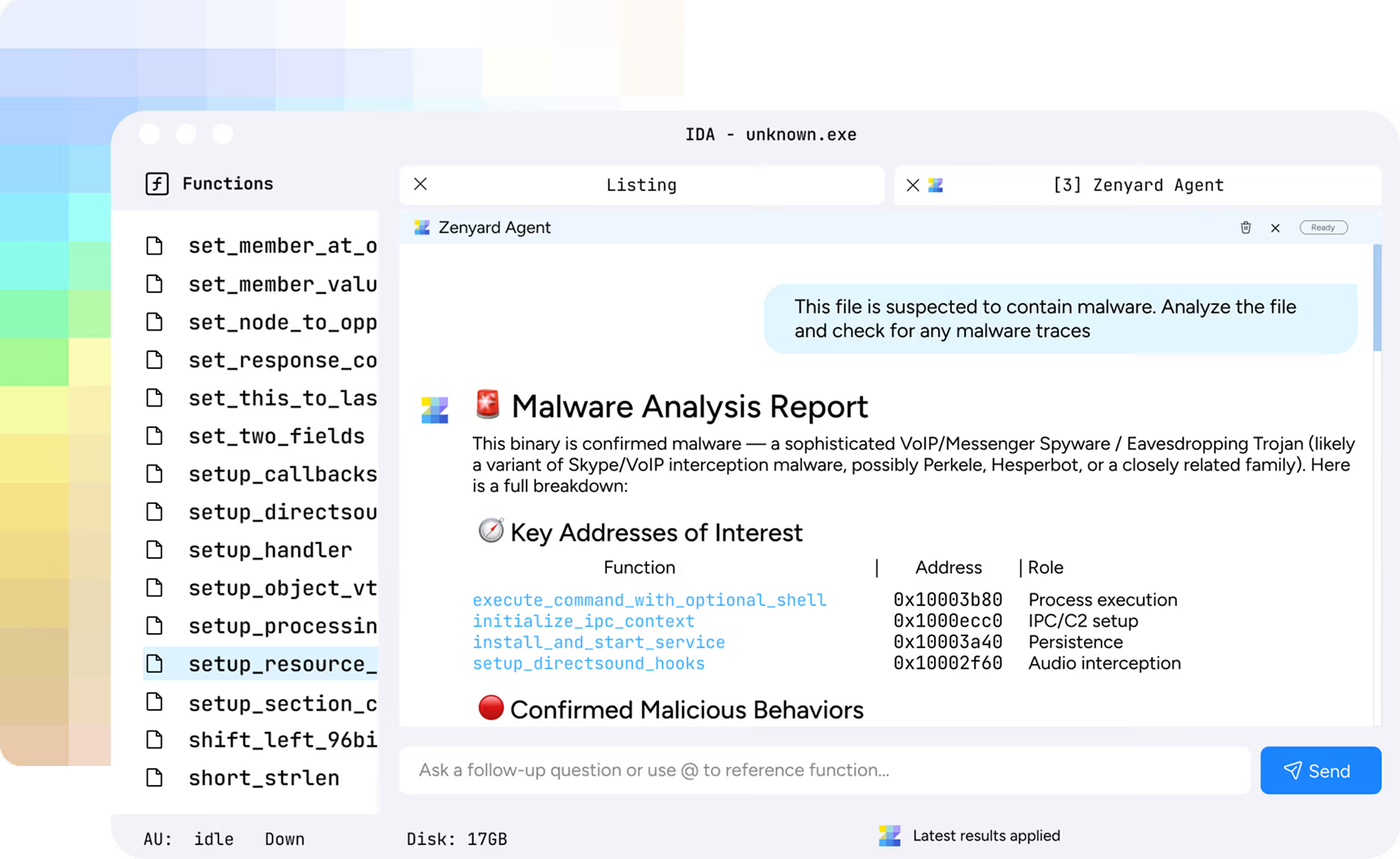
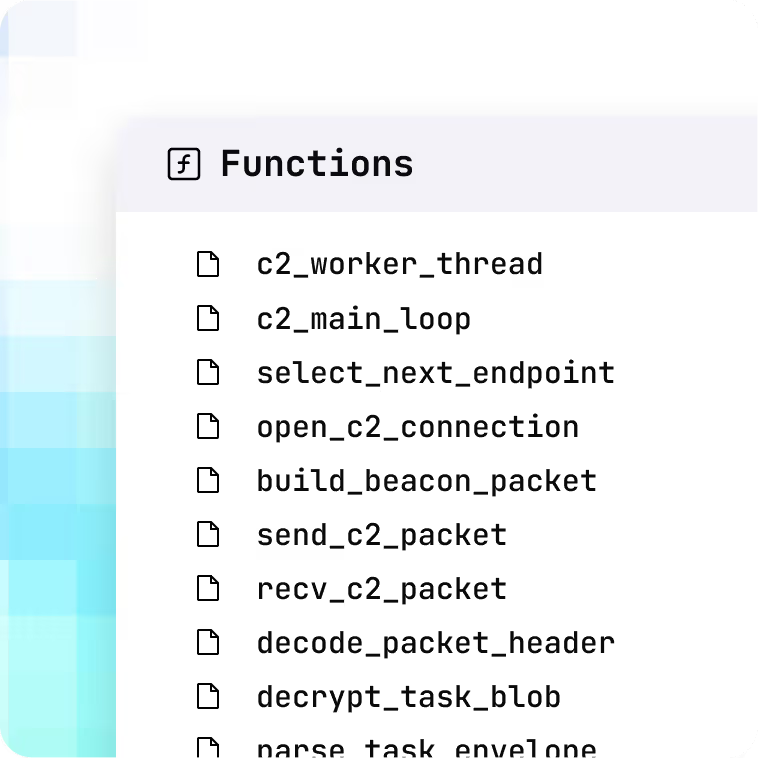
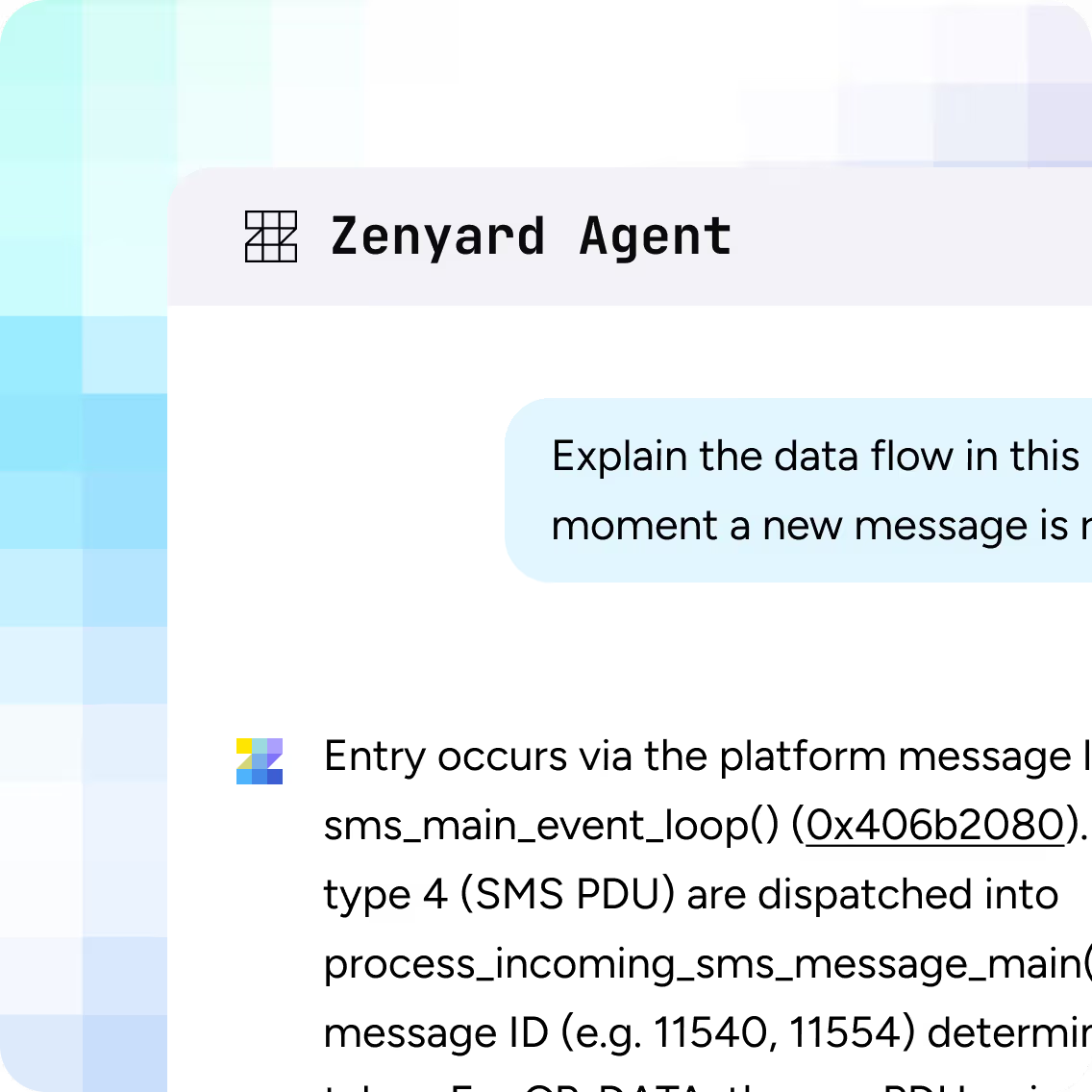
Zenyard helps malware analysts and threat research teams analyze more malware in less time. Using purpose-built AI agents that analyze entire files end-to-end, it uncovers core capabilities, payload logic, C2 communication patterns, and indicators of compromise, so teams can understand each malware sample much faster.
Deploy Zenyard Securely, Your Way
Deploy fully on-premises, even within air-gapped networks
Deploy within your own fully controlled cloud environment
The New Way to Reverse Engineer
Captures critical context
across entire malware binaries
end-to-end
Turns stripped binaries
into fully named, documented, source-like code
Automates data layout recovery
with whole-program struct
reconstruction
Enables effective navigation
handle Go and Rust binaries with purpose-built AI agents
Maps malicious behavior
across the binary with agent-driven exploration
Surfaces relevant code paths
and attack surfaces
in minutes
Reduce Time to Insight Across Malware Analysis Workflows
Comprehensive end-to-end file understanding

Improved code readability through naming, documentation, and struct reconstruction

Support for common malware languages such as Rust and Go
Direct integration with existing decompilers
Automated malware triage through agent-based binary exploration