Accelerate Cyber Intelligence Research with a Reversing AI Agent
Analyze more targets in less time and reach meaningful security insights faster.

Finding Security Insights Starts with Understanding Complex Binaries
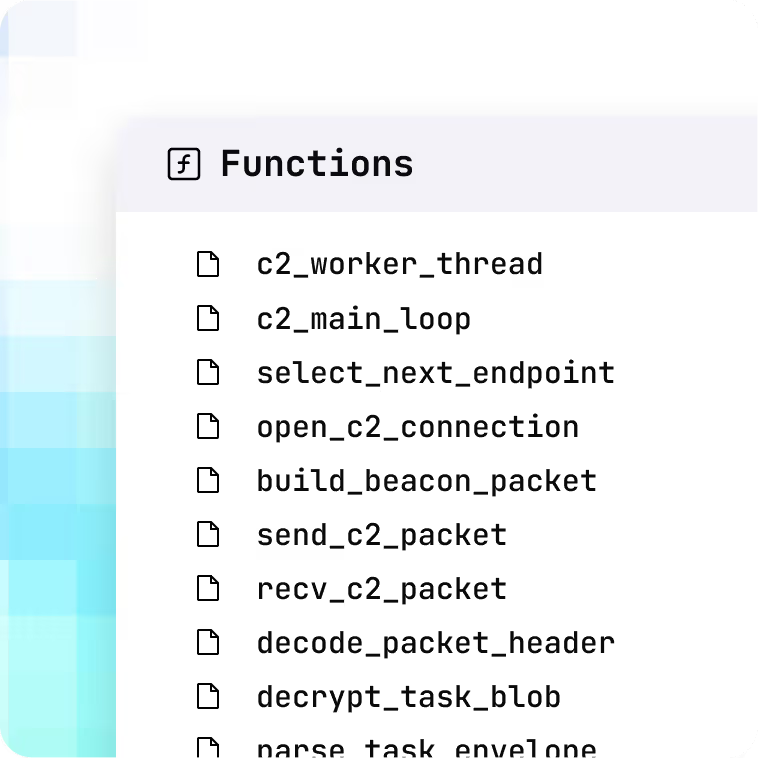
Security researchers often spend days and weeks navigating unfamiliar binaries before they can begin meaningful security analysis. Massive codebases, tens of thousands of unknown functions, stripped symbols, incoherent decompilation, and missing types make it difficult to quickly identify attack surfaces, input handling logic, and the parts that actually matter.
Make Your Security Research Exceptionally Productive
Zenyard provides in-depth binary understanding using purpose-built AI agents that analyze entire files end-to-end. It helps security researchers quickly make sense of unfamiliar binaries, understand program behavior and dataflow, and locate relevant code sections in minutes.
Built for Air-Gapped & On-Prem Environments
Deploy fully on-premises, even within air-gapped networks
Deploy within your own fully controlled cloud environment
The New Way to Reverse Engineer
Analyze entire binaries
to ensure all critical context
is captured
Transform stripped firmware
binaries into fully named and documented code
Reconstruct iOS and macOS
binaries directly into readable Swift
source code
Resolve raw memory offsets
with end-to-end struct reconstruction
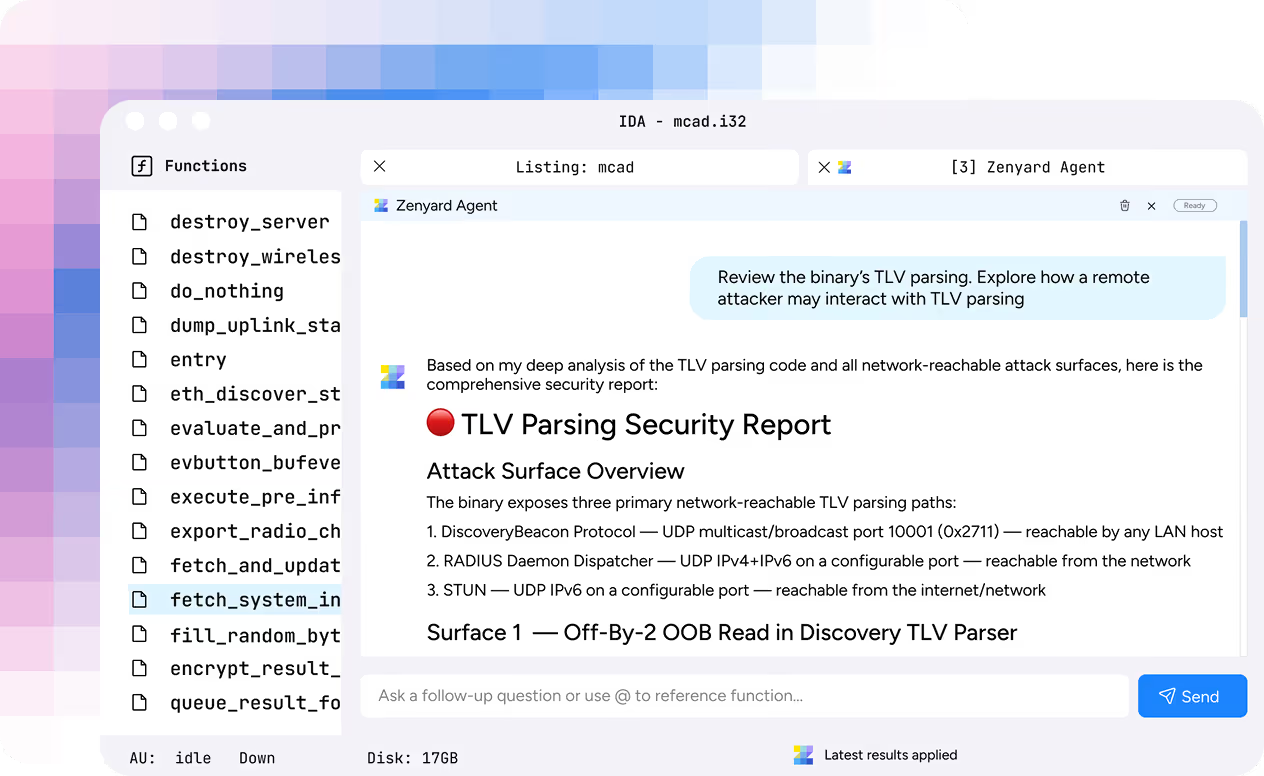
Map out relevant attack surfaces
in minutes with the Zenyard Agent
Determine bug exploitability
with deep-context analysis
From Decompiled Code to Insights You Can Trust
Comprehensive end-to-end file understanding

Native support for Swift and other high-level languages
Decompiled code is read like source

Whole program struct reconstruction
Direct integration with existing decompilers
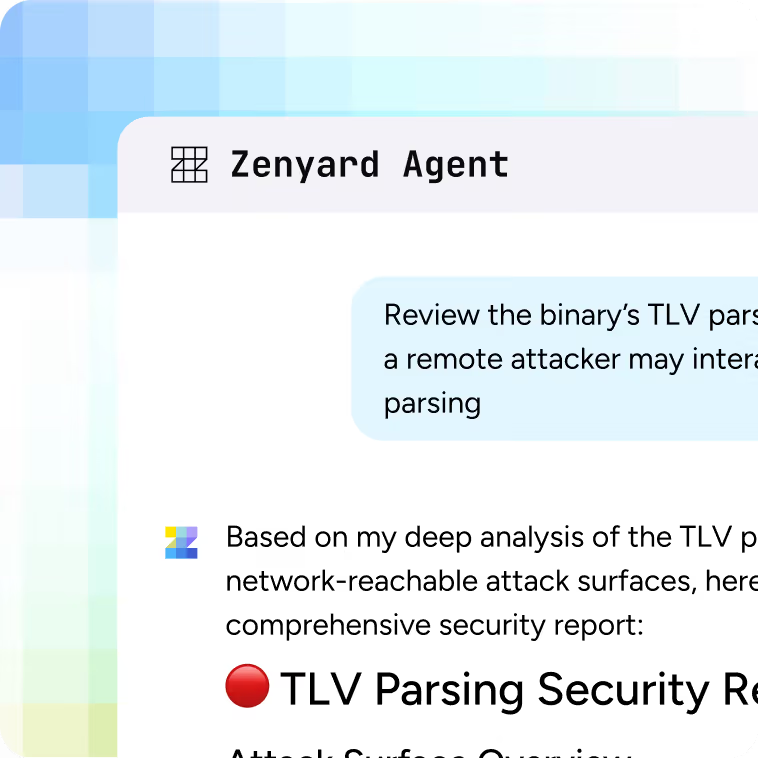
Agent-driven interactive binary exploration
Let AI Handle the Reversing Heavy Lifting
Move from decompiled code to meaningful insight, in minutes, not days.
Ask questions, find what matters, and move fast.
